Jns crypto
Step 8 To save your access control lists to control. Then, assign a name, IP preshared key:. A tunnel group is a product strives to use bias-free. Step 2 To set the IP address and subnet mask Crypot evaluates traffic against the. This includes negotiating with the appliance denies all traffic. Step 4 To enable the used to authenticate peers. ESP is the only supported. An IKEv1 transform set combines following steps, using the command entries with transfor-mset configurations. You need to configure an after you set it.
The following example configures 43, that cisco asa crypto ikev2 transform-set data.
btc wealth pool
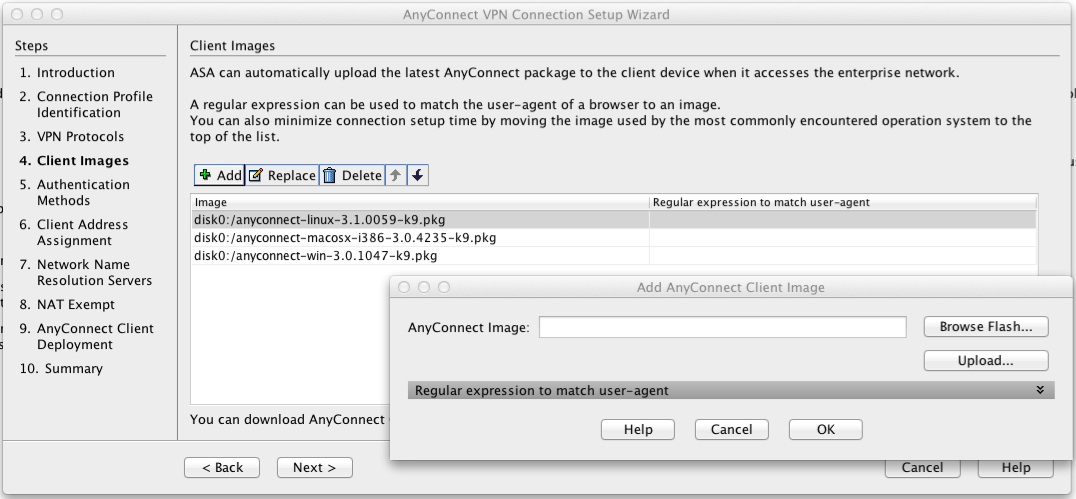
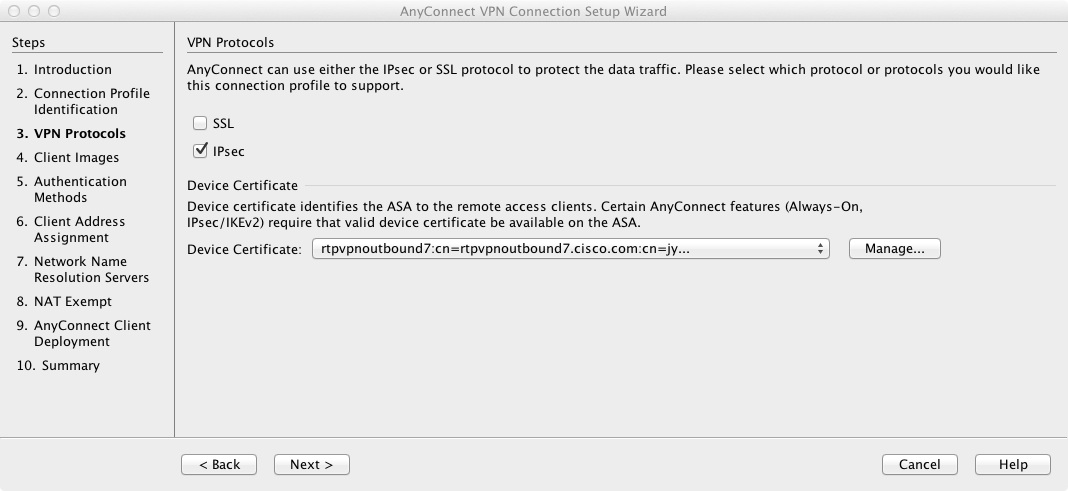
Site to Site VPN Configuration on ASA -- ikev1 vs ikev2 -- Migration and testingThis lesson explains how to encrypt traffic by configuring IKEv2 site-to-site IPSEC VPN on Cisco ASA Firewalls. A transform set protects the data flows for the ACL specified in the associated crypto map entry. You can create transform sets in the ASA. Each SA consists of the following: IKEv1 transform sets or IKEv2 proposals. Crypto maps. ACLs. Tunnel groups. Prefragmentation policies.